Does Google use JWT

NameDescriptionassertionThe JWT, including signature.
Does Google use Auth0?
Use Auth0 with Google Sign-In, which is a secure authentication system that reduces the burden of login for your users, by enabling them to sign in with over 1.5B existing Google Accounts—the same account they already use with Gmail, Play, and other Google services. …
Does Google use OAuth?
Google APIs use the OAuth 2.0 protocol for authentication and authorization. Google supports common OAuth 2.0 scenarios such as those for web server, client-side, installed, and limited-input device applications. To begin, obtain OAuth 2.0 client credentials from the Google API Console.
Where are JWT used?
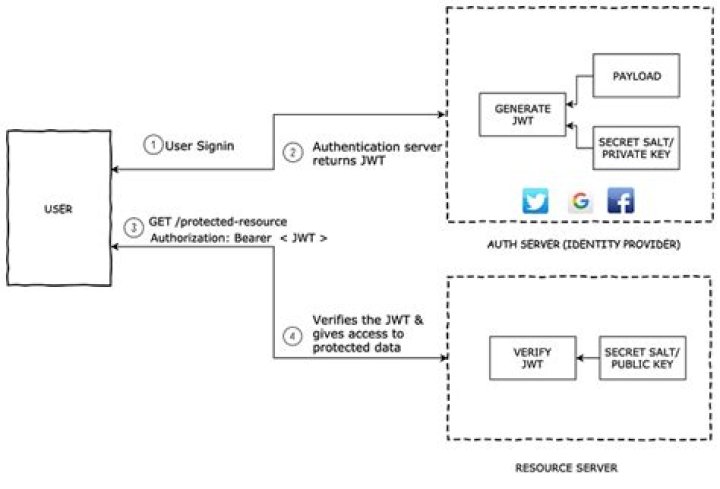
The tokens are designed to be compact, URL-safe, and usable especially in a web-browser single-sign-on (SSO) context. JWT claims can typically be used to pass identity of authenticated users between an identity provider and a service provider, or any other type of claims as required by business processes.Is OAuth2 same as JWT?
JWT and OAuth2 are entirely different and serve different purposes, but they are compatible and can be used together. The OAuth2 protocol does not specify the format of the tokens, therefore JWTs can be incorporated into the usage of OAuth2.
Is it safe to use Auth0?
Auth0 is a secure and universal service which ensures authentication and authorization functionality.
Is Google OAuth API free?
3 Answers. Google Sign-in is free. No pricing.
How is JWT validated?
- Verify that the JWT contains three segments, separated by two period (‘. …
- Parse the JWT to extract its three components.
Is JWT URL safe?
A JWT is URL-encoding-safe. There will be no data-loss when used in-place; no additional encoding is required; it is even URL encoding safe inherently, applying url-encoding (percentage-encoding) on the JWT multiple times will not destroy it.
When did OAuth2 come out?In July 2007 the team drafted an initial specification and the group was opened to anyone interested in contributing. On October 3rd, 2007 the OAuth Core 1.0 final draft was released.
Article first time published onIs Google SSO OAuth?
Google Sign-In manages the OAuth 2.0 flow and token lifecycle, simplifying your integration with Google APIs. A user always has the option to revoke access to an application at any time.
Can redirect URI be localhost?
http URI schemes are acceptable because the redirect never leaves the device. As such, both of these URIs are acceptable:
How do I get Google OAuth?
- Go to the Google Developers Console.
- Navigate to the tab “Credentials”.
- Click Select a project >> New Project and then click the button “Create”.
- Navigate to the tab “OAuth consent screen”.
- Enter the Application name, Authorized domains and click the button “Save”.
Can JWT be used without OAuth?
Don’t Leave JWT All Alone The simple fact is that JWTs are a great solution, especially when used in tandem with something like OAuth. Those benefits quickly disappear when used alone, and in many cases can result in worse overall security.
Does SAML use JWT?
Both are used for Exchanging Authentication and Authorization data between parties, but in different format. SAML is a Markup Language(like XML) and JWT is a JSON.
What can I use instead of a JWT?
- OAuth2. …
- Passport. …
- Spring Security. …
- Auth0. …
- Amazon Cognito. …
- Keycloak. …
- Firebase Authentication. …
- Devise.
What is Auth0 vs OAuth?
OAuth 2.0 is a protocol that allows a user to grant limited access to their resources on one site, to another site, without having to expose their credentials. Auth0 is an organisation, who manages Universal Identity Platform for web, mobile and IoT can handle any of them — B2C, B2B, B2E, or a combination.
Is Gmail API free?
The Gmail API, like Gmail itself, is (currently) a free service from Google. There are quota (usage) limits on the API. For client-secrets. json (credentials used for server-to-server authentication), there is no expiration.
How much is Google SSO?
How much does it cost? Google Cloud Identity has a free plan with basic SSO and MFA features, and the Premium plan, which includes a unified management console and service-level agreement (SLA), is $6/month per user.
Why is Auth0 so expensive?
Auth0’s main product is for managing public user access to your app. … Of course it can also just authenticate users, but that’s a tiny part of the functionality which is why it is so much more expensive.
Is Auth0 a Fedramp?
— July 31, 2018 — Auth0, a global leader in Identity-as-a-Service (IDaaS), today announced it has achieved ISO 27001:2013 and ISO 27018:2014 certification, signifying Auth0’s ongoing commitment to providing its customers with the highest standards for information security.
How do you pronounce Auth0?
Auth0, pronounced “auth-zero,” has been described as like Stripe for payments or Twilio for messaging.
Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
Can JWT be stolen?
Generally speaking, this is nice, but what happens if your entire JWT is stolen? Because JWTs are used to identify the client, if one is stolen or compromised, the attacker has full access to the user’s account in the same way they would if the attacker had compromised the user’s username and password instead.
How JWT is used in API security?
JWT has a collection of data and it allows the API to transfer only secured data. JWT asserts identity associated with trust between the two communicating parties. The interactive application development helps to secure apps and enable secure interactions within applications. JWT helps to create and use tokens.
How can I get JWT token from browser?
- From the navigation menu, select Applications. On the Applications page, select your application. Then select the Details tab.
- Make note of the Client ID and retrieve the Client Secret from your tenant administrator. WARNING:
What is JWT kids token?
kid is an optional header claim which holds a key identifier, particularly useful when you have multiple keys to sign the tokens and you need to look up the right one to verify the signature. Once a signed JWT is a JWS, consider the definition from the RFC 7515: 4.1.4. ” kid” (Key ID) Header Parameter.
Is JWT case sensitive?
This name is case sensitive. Names may not match other registered names in a case-insensitive manner unless the Designated Experts state that there is a compelling reason to allow an exception.
Is OAuth slow?
0 authorization micrservice is extremely slow. It takes 450+ms to check a token. Generating tokens takes 1.6s and above.
Does Okta use OAuth?
Okta is a standards-compliant OAuth 2.0 authorization server and a certified OpenID Connect provider . … The OAuth 2.0 protocol provides API security via scoped access tokens, and OpenID Connect provides user authentication and single sign-on (SSO) functionality.
Who created OAUTH2?
OAuth began in November 2006 when Blaine Cook was developing the Twitter OpenID implementation.