Does JWT protect against CSRF
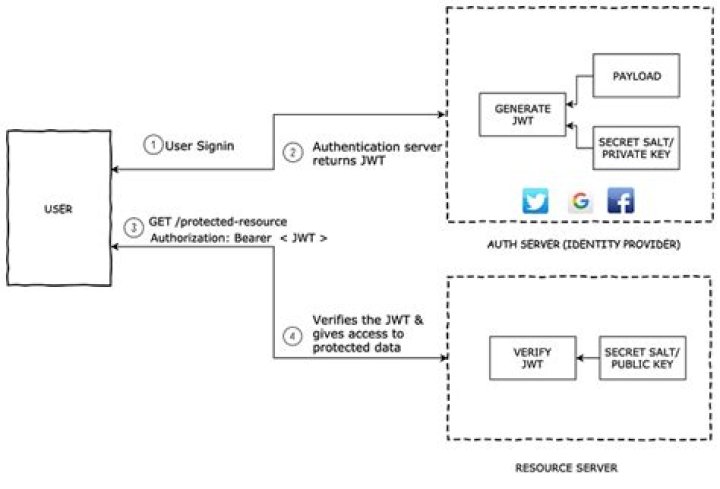
If you put your JWTs in a header, you don’t need to worry about CSRF. You do need to worry about XSS, however. If someone can abuse XSS to steal your JWT, this person is able to impersonate you.
Can JWT prevent CSRF?
If you put your JWTs in a header, you don’t need to worry about CSRF. You do need to worry about XSS, however. If someone can abuse XSS to steal your JWT, this person is able to impersonate you.
Does SSL protect against CSRF?
5 Answers. No, running a page on HTTPS does not protect it from CSRF. The fact that the communications between the browser and server is encrypted has no bearing on CSRF.
What defense prevents CSRF?
Preventing CSRF attacks The most robust way to defend against CSRF attacks is to include a CSRF token within relevant requests. The token should be: Unpredictable with high entropy, as for session tokens in general. Tied to the user’s session.Is JWT safe for authentication?
JWTs can be used as an authentication mechanism that does not require a database. The server can avoid using a database because the data store in the JWT sent to the client is safe.
Can CSRF happen without cookies?
CSRF tokens prevent CSRF because without token, attacker cannot create a valid requests to the backend server. CSRF tokens should not be transmitted using cookies. The CSRF token can be added through hidden fields, headers, and can be used with forms, and AJAX calls.
Does Authorization header prevent CSRF?
This is a type of HTTP authentication where the user is identified through a token that is submitted in “Authorization” header of each request. This mechanism solves CSRF because unlike cookies it is not submitted by the browser automatically.
Can CSRF token be stolen?
Cross-Site Request Forgery (CSRF) is an attack that forces an end user to execute unwanted actions on a web application in which they’re currently authenticated. CSRF attacks specifically target state-changing requests, not theft of data, since the attacker has no way to see the response to the forged request.How do I disable CSRF protection in Jenkins?
Disabling CSRF Protection To disable CSRF protection, set the system property hudson. security. csrf. GlobalCrumbIssuerConfiguration.
What can I do with CSRF token?CSRF tokens can prevent CSRF attacks by making it impossible for an attacker to construct a fully valid HTTP request suitable for feeding to a victim user.
Article first time published onWhy is CSRF difficult to detect?
The apparent validity of CSRF traffic makes is difficult to block. Web developers must protect their sites by applying measures beyond authenticating the user. After all, the forged request originates from the user even if the user isn’t aware of it. Hence, the site must authenticate the request and the user.
What is anti forgery in MVC?
To help prevent CSRF attacks, ASP.NET MVC uses anti-forgery tokens, also called request verification tokens. The client requests an HTML page that contains a form. … One token is sent as a cookie. The other is placed in a hidden form field. The tokens are generated randomly so that an adversary cannot guess the values.
What is the difference between XSS and CSRF?
What is the difference between XSS and CSRF? Cross-site scripting (or XSS) allows an attacker to execute arbitrary JavaScript within the browser of a victim user. Cross-site request forgery (or CSRF) allows an attacker to induce a victim user to perform actions that they do not intend to.
Why is JWT not safe?
If someone modifies the data contained in the JWT, the server will fail to decode it. So the server can trust any JWT that it can decode. However, if a hacker got access to your computer, they could see the JWT that is stored in the browser and use it.
Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
When should you not use JWT?
Although JWT does eliminate the database lookup, it introduces security issues and other complexities while doing so. Security is binary—either it’s secure or it’s not. Thus making it dangerous to use JWT for user sessions.
How can cross site request forgery CSRF be prevented?
Validating Requests. Attackers can perform a CSRF attack if they know the parameters and values to send in a form or in a query string. To prevent those attacks, you need a way to distinguish data sent by the legitimate user from the one sent by the attacker.
Do you need CSRF?
So, as a rule of thumb, whenever you use cookies and sessions for requests to validate a user, i.e. to confirm or establish trust in a user, use CSRF protection. Since you want to establish trust in your user when he signs up, the same applies.
Is CSRF token a cookie?
The CSRF token in fact could be the standard authentication cookie when using this method, and this value is submitted via cookies as usual with the request, but the value is also repeated in either a hidden field or header, of which an attacker cannot replicate as they cannot read the value in the first place.
How do I get my CSRF token?
1) In Chrome/Firefox, open the console by right clicking anywhere and chose “inspect”(for Chrome) or “inspect element”(for Firefox). Do a get request or login first while you see the request made , to get CSRF-TOKEN sent from the server. 5) In the next post request, use the CSRF-TOKEN from the previous request.
How do I make a Csrftoken?
- Use a well-established random number generator with enough entropy.
- Make sure tokens can’t be reused. …
- Verify the received token is the same as the set token in a safe way, for example, compare hashes.
- Do not send CSRF tokens in HTTP GET requests.
How do I get Jenkins crumb data?
Generate an API token by going your Jenkins home page > your name in the top right corner click > Configure > “Add new token”. Copy this token. In Intellij Settings > Tools > Jenkins Plugin, fill in server address and username. For password, put in the token copied in step 1 and leave the “crumb data” section empty.
How can I get Jenkins crumb value?
GOTO: Jenkins > Manage Jenkins > Configure Global Security and enable Prevent Cross Site Request Forgery exploits . Select Default Crumb Issuer from Crumb Algorithm and save to apply changes and enable.
What is crumb issuer in Jenkins?
Description. The Strict Crumb Issuer plugin is an extended version of the Default Crumb Issuer embedded in Jenkins core. It provides advanced options of configuration. It’s strongly recommended to use a Crumb Issuer (this one or the embedded one), otherwise your instance will not be protected against CSRF attacks.
What is CORS and CSRF?
CSRF is a vulnerability and CORS is a method to relax the same-origin policy. CORS is something you might want to use (in certain circumstances) whereas CSRF is an undesirable design mistake. There are vulnerabilities associated with the CORS mechanism.
What does CSRF stand for?
Cross-Site Request Forgery (CSRF) is an attack that forces authenticated users to submit a request to a Web application against which they are currently authenticated. CSRF attacks exploit the trust a Web application has in an authenticated user.
Why is CSRF important?
Why CSRF is important CSRF attacks can be used on a huge array of sites. If a site allows data to be altered on the user side, then it is a potential target for an attacker. With some of the fixes listed, above, your website can guarantee a much higher level of security.
How do I fix CSRF verification failed aborted?
- Disable autofill, allow cookies, and clear your cache.
- Reset your password using Chrome.
How does CSRF work in Spring Security?
CSRF (Cross Site Request Forgery) is a technique in which an attacker attempts to trick you into performing an action using an existing session of a different website. Spring Security when combined with Thymeleaf templates, automatically inserts a token into all web forms as a hidden field.
Which threat is most likely to occur when a Web application fails to validate a clients access to a resource?
Cross-Site Scripting (XSS) attacks occur when: Data enters a Web application through an untrusted source, most frequently a web request. The data is included in dynamic content that is sent to a web user without being validated for malicious content.
Which threat can occur when a Web application fails to validate a client's access to a resource?
The SSRF Attack To execute a Server-Side Request Forgery (SSRF) attack, the attacker abuses the functionality on the server to read or update internal resources. SSRF occurs when a web application fails to validate user input when fetching a resource.